“Organic solidarity is a social cohesion based upon the interdependence that arises between people from specialization of work and complementarianism as result of more advanced (i.e., modern and industrial) societies. Although individuals perform different tasks and often have different values and interests, the order and very solidarity of society depend on their reliance on each other to perform their specified tasks” Source Durkheim, Wikipedia.
Blockchain invariably lends itself to a discussion about the esoteric ideas of Coins, NFT’s and creation of Digital assets. Assetization and property rights are the core of a market economy that allows rights to be exchanged at a fair market value (whatever the market construes as fair). The overhang of the origins of blockchain in the mutual need for a coin that maintains the fidelity of the chain and vice-versa tends to ignore the larger universe of applications that are mundane but critical to commerce and all human interactions that link us to systems that automate/animate our lives.
Trust is a necessary condition that allows billions of people to interact, networks to form, commerce to flow and gains to be made and distributed- is what makes the economy move seamlessly – the sociologist Simmel linked time to money as he analysed the peculiarities of modern life circa 1858 –
“If all clocks and watches in Berlin would suddenly go wrong in different ways, even if only by one hour, all economic life and communication of the city would be disrupted for a long time”
– Georg Simmel
Indeed, trust is what drives our ability to wake up and switch on the power, use medicines, turn on the tap and use the elevator, take a cab to work, use office equipment, mostly seamlessly. The ‘engineering trust‘ that is engendered in objects is increasingly a subject of scrutiny – for reasons of provenance, sustainability, composition, method of extraction, quality of labour practices etc., With it comes the ubiquitous necessity to check the veracity of individuals and organizations that make as well as certify claims to expertise, track record, experience, health etc.,– in a world of networks that makes these judgements by triangulating over ever-expanding networks of people and objects. It is the presumption of certainty that allows us to live our quotidian lives with a large degree of assured confidence in the choices we make and the consequences we seek.
“Life is intrinsically, well, boring and dangerous at the same time. At any given moment the floor may open up. Of course, it almost never does; that’s what makes it so boring”
– Edward Gorey
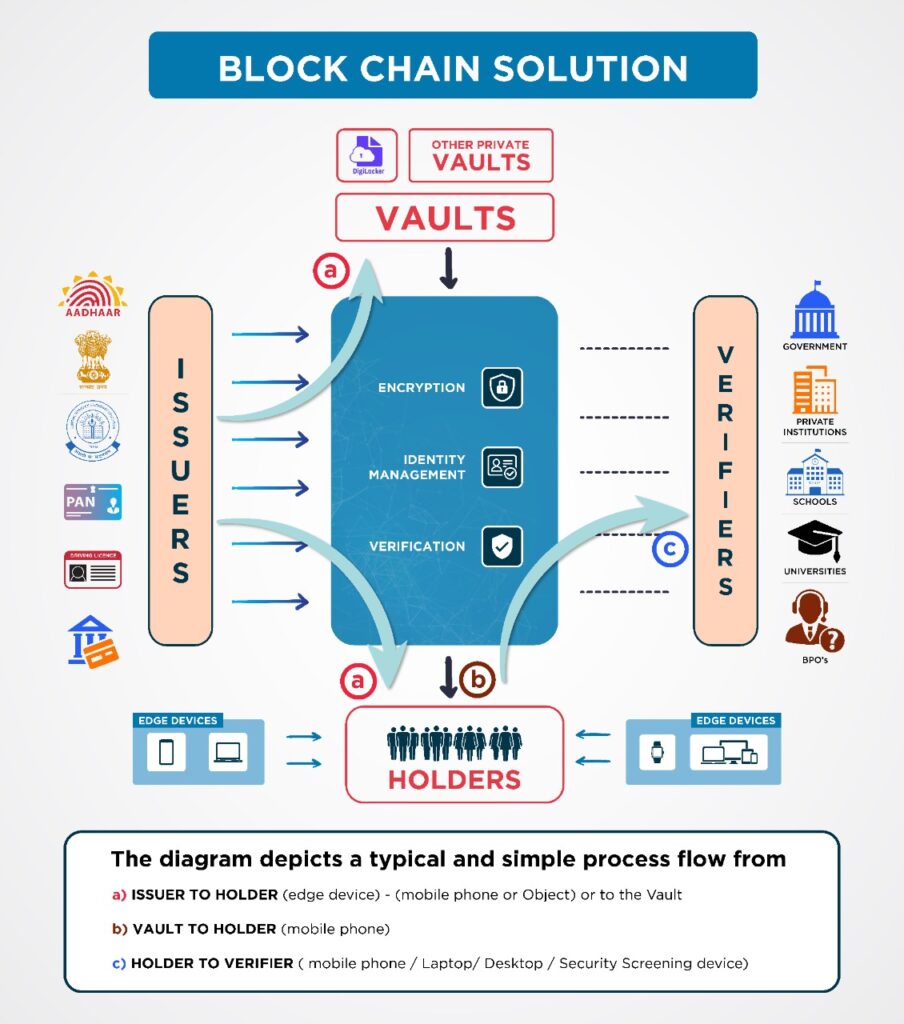
What are the main components of a Blockchain Solution?
What makes the blockchain vital is its ability to trace provenance and allow a non-intermediated self-authenticated individually purposed use of credentials, for individuals. For objects, it allows a granular trace of all its component certifications of authenticity/characteristics. In a previous article Blockchain, a Billion and Bureaucracy we took a view on disintermediation that is enabled by the blockchain. In this post, let us look at the component parts of a blockchain-based system that allow an individual to purpose the use of his self-authenticated, non-repudiable and tamper-proof credentials.
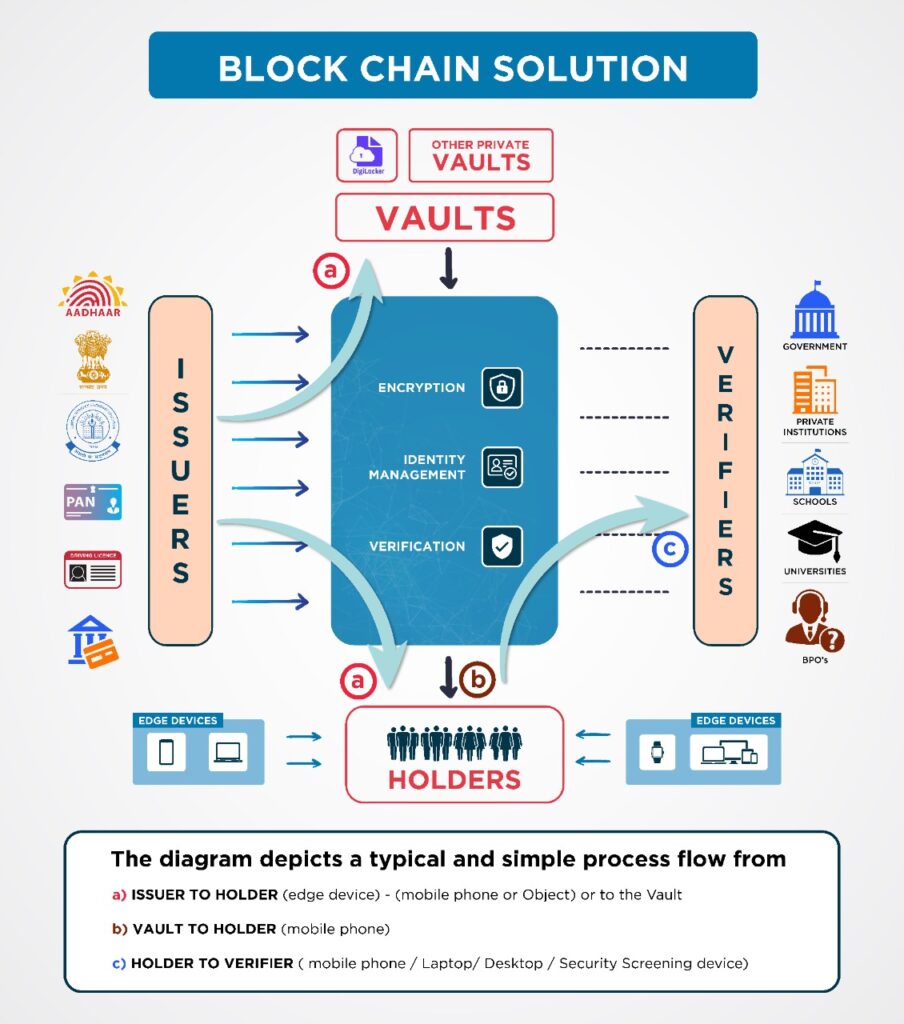
Blockchain systems are of various forms, and many inhabit purely private networks. There are also quasi-public networks and purely public networks. Depending on the kind of utility it serves, the blockchain can store data (as in a bank balance). However, many credential transaction applications can use an identity management system that authenticates using only cryptographic equivalents, and not the raw data itself (the data rests only at the Vault or at the user’s edge device).
Issuers: These are organizations that issue credentials to people and objects. Aadhaar is an issuer of foundational identity – the identity that an individual is provided by virtue of being herself/himself. Issuers can be from the private sector or government ex. A PAN Card or an employee identity card from an auto company, the auto company can give an identity to a manufactured car, a pharmaceutical company to a batch of medicine.
Vaults: These are secure locations that store the individual’s data securely. While organizations may store data on individuals within, they may also use a commercial private vault to securely store the data. Vaults can be a consortium or private entities. For instance, a consortium can store Doctors graduation records across countries and different types of medical institutions and degrees awarded. These Vaults can then commercially offer services to potential hospitals and medical schools to source/deliver authenticated blockchained records, by permission.
Holders: These are individuals who use edge devices, that hold their personal records, that have been downloaded from vaults like the DigiLocker or directly from issuers. The individual then uses these credentials in situations that require the transmission of credentials for the purpose of delivering authentic information, requiring access to restricted areas etc. Holders can also be objects that can provide privately or broadcast privately the information they hold. A car can privately provide information of its component parts to the manufacturer or the owner as the case may require. Also, a batch of medicine can broadcast its provenance to anybody scanning the content of the label. This can include a source of ingredients etc., supply chains will use object provenance of component parts.
Verifiers: These are organizations or individuals that scrutinize or use the data for personal or professional use. For instance, a security agency verifying an Aadhaar card. An individual verifying the source of components in his car or the source of ingredients in his medicine.
How will this set of components change if the blockchain application supports Objects in a Supply Chain?

Can we rework this blockchain diagram to create the high-level components of a Migrant Worker Support System, using identity and location based information?

How do the blockchain components look, if Aadhaar is used to create a “Emergency Response System”?

*The author of this post – KP Vinod, is an Advisor at Dhiway. He has a background in leadership roles in Marketing and Alliances with SAP, CA and is an MPA from the Lee Kuan Yew School of Public Policy, NUS.
